-
Manually Enroll Windows Device Into Autopilot
Assumptions
- You have a Windows 11 PC at the Out-Of-Box-Experience (OOBE)
- Your organization has an Intune subscription
- You have Entra ID permissions to add a device to Windows Autopilot (e.g. Intune Administrator)
- You have an USB storage device to save the Diagnostic logs
This is a restatement of the process outlined by Microsoft1. Those instructions lack a clear visual for navigating Intune.
Microsoft recommends that this method only be used for testing or other limited scenarios.
Read more… -
Specify Hugo Version In Netlify
Thinkinginbytes.com is generated using Hugo and hosted by Netlify. Netlify watches the site’s repo on Github and commits trigger a site build process. I’ll post more details about hosting a Hugo site with Netlify later. Site development is local. To view the site on a local machine, Hugo must be installed. It is likely that your local version of Hugo is versions ahead of the default Netlify Hugo version. This version mismatch may cause Netlify builds to fail. You may need to specify which version of Hugo you want Netlify to use.
Read more… -
Thoughts On Choices And Life
Occasionally, I see a social media post123 re-quoting:
Read more…Hard Choices, Easy Life
Easy Choices, Hard Life -
Proving Congruence For Fun
Background
I want to understand the math behind asymmetric cryptography.1 This field relies heavily on Modular Arithmetic.2 I bought an undergraduate math textbook for self-study. This article is a record of a proof exercise in the book. It is also a good exercise in writing math equations using LaTeX.
Read more… -
A Piecewise Hashing Example
- The Problem
- Cryptographic Hashing
- What Is Piecewise Hashing
- The Obvious Weakness
- Final Thoughts
- References
NOTE: ChatGPT was used to create some portions of the code in this article. The words are mine.
The Problem
When cybersecurity analysts find malicious files, they share their finding with the greater security community. They run the file through a cryptographic hashing function and share the results of this function, called a hash. The hash is a kind of fingerprint that identifies the file based on the information contained in the file. Others can look through their environments, hash their files, and compare the results to hunt for the malicious file.
Read more…
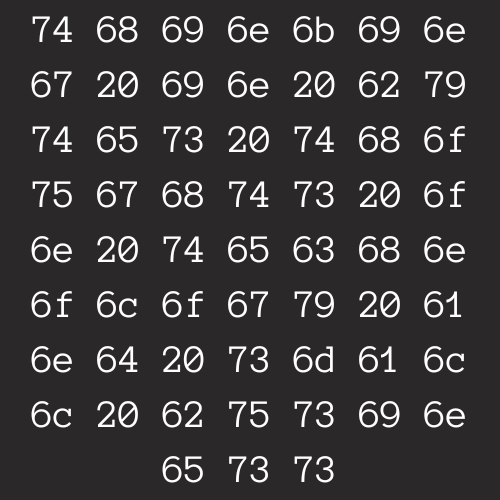
Thinking In Bytes
Thoughts On Technology And Small Business